“Don’t click on a link received through an email from any unknown person”. If you click, the hacker will gain access to your system and you will be a victim of cybercrime.
This simple technique, known as Spear phishing, was used last year to gain access to a $10bn US hedge fund’s high-frequency trading (HFT) system. The hacker put a chain of command-and-control channels that slowed the system down by fractions of a second, eventually leading to multi-million dollar losses.
Hedge Funds, Banks and Financial services are under constant threats of cyberattack. Some of the most prominent examples of the wide-ranging and potentially devastating effects that can result from cyber-attacks are the December 2013 data breach of Target Corporation affecting 40 million Target customers’ payment card data.
The level of this threat has become critical and continues to rise. The importance of this issue is also evident from the recent talks between the Heads of two powerful nations the U.S. and U.K. below:
“We must work together to defend ourselves from new threats like cyber-attacks. This is an evolving threat which poses a real risk to our businesses and that’s why we’re taking our cooperation with the U.S. to an unprecedented level. This is about pooling our effort so we stay one step ahead of those who seek to attack us” UK Prime Minister David Cameron said in a statement while holding talks with U.S. President Barack Obama.
Cyberbreach is a reputational risk that can create irreparable brand damage for a hedge fund. Let us have some insights into the growing threat of cyber-attacks, as well as the ways to prevent, respond to, and mitigate the risks of such attacks.
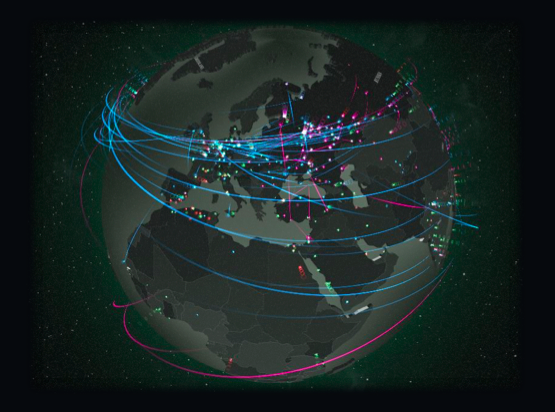
A report based on survey of exchanges across the world, ‘Cyber-crime, Securities Markets and Systemic Risk’, reveals one out of every two exchanges had been subject to a cyber-attack over the preceding 12 months. The SEC and other regulators have increased the regulatory emphasis on cybersecurity. But cybersecurity should not be viewed mainly as a compliance concern, ignoring the real threat. Hackers infiltrate networks and gain access to sensitive information. It is necessary to protect proprietary and confidential organization information as well as clients’ information. The consequences of leak-out of clients’ sensitive data may be beyond imagination.
Take proactive measures like educating own employees about Spear phishing. Hacker explores selected individuals’ profiles on social media such as Facebook, LinkedIn and Twitter to tap on personal and sensitive information. Then the hacker uses them to mirror familiar email addresses, dialect and URLs in their messages and ultimately better deceive users. Variables that differ between authentic and fraudulent may be even only one special character, alphabet or number. Create Information Security Awareness among employees. There is need to be more conscious and double check while opening emails, connecting to networks or downloading. The attacks may result into denial-of-service to customers, phishing, malware and software vulnerabilities.
Managers should put in place preventive, detective and corrective controls. They need to invest in latest anti-virus and anti-malware software as well as network firewalls to mitigate the risks, strengthen security measures. Implement layers of verification and authorisation to reduce the likelihood that the system will be breached. Conduct mock tests and system audit periodically. Detective control helps identify and give signal whenever preventative controls are bypassed. This enables to activate response plan early before much harm is done. Managers should make sure they have effective business continuity plans (BCP) and disaster recovery (DR) systems in place.
Hedge funds need to focus not only on outside hackers but also to protect systems from insiders. Cyber risk is also from insiders including contractors’ and vendors’ employees. Proper safeguard is needed against security risks that could arise from vendors having access to the hedge fund systems.
Cyber-crime is rapidly becoming a threat and fund managers can no longer afford to ignore. Managers must take adequate measures to mitigate the risk of cyber-threats. Hedge Funds should have business continuity and disaster plans in place to face, if any, loss due to a data breach. Effective corrective measures limit technical, business, reputational and legal damages.

Peyman Khosravani is a global blockchain and digital transformation expert with a passion for marketing, futuristic ideas, analytics insights, startup businesses, and effective communications. He has extensive experience in blockchain and DeFi projects and is committed to using technology to bring justice and fairness to society and promote freedom. Peyman has worked with international organizations to improve digital transformation strategies and data-gathering strategies that help identify customer touchpoints and sources of data that tell the story of what is happening. With his expertise in blockchain, digital transformation, marketing, analytics insights, startup businesses, and effective communications, Peyman is dedicated to helping businesses succeed in the digital age. He believes that technology can be used as a tool for positive change in the world.